RSA私鑰檔案(PEM-PKCS#1)解析
在PKCS#1 RSA演算法標準中定義RSA私鑰語法
RSAPrivateKey ::= SEQUENCE {
version Version, //版本
modulus INTEGER, // RSA合數模 n
publicExponent INTEGER, //RSA公開冪 e
privateExponent INTEGER, //RSA私有冪 d
prime1 INTEGER, //n的素數因子p
prime2 INTEGER, //n的素數因子q
exponent1 INTEGER, //值 d mod (p-1)
exponent2 INTEGER, //值 d mod (q-1)
coefficient INTEGER, //CRT係數 (inverse of q) mod p
otherPrimeInfos OtherPrimeInfos OPTIONAL
}
otherPrimeInfos 按順序包含了其它素數r3, …, ru的資訊。如果version是0 ,它應該被忽略;而如果version是1,它應該至少包含OtherPrimeInfo的一個例項。
OtherPrimeInfos ::= SEQUENCE SIZE(1..MAX) OF OtherPrimeInfo
OtherPrimeInfo ::= SEQUENCE {
prime INTEGER, //ri – n的一個素數因子ri ,其中i ≥ 3
exponent INTEGER, //di – di = d mod (ri ? 1)
coefficient INTEGER //ti – CRT係數 ti = (r1 · r2 · … · ri–1)–1 mod ri
}
RSAPrivateKey 和OtherPrimeInfo各域的意義,如註釋所示。
本文講述適用範圍:已知各域值,組裝RSA私鑰檔案,即PEM檔案。
PEM檔案組成是TLV結構。
一、資料例項,各域值如下:
- version:
00 - moudlus:
c1f7f7196d9ef4b97abede2d5322d76c17fdf9592c39511027268293a14603b6
5d5425c99cfb5194d37b73487d26e31edf35cfe1e7f58366b5adb35d18f8cdb1
401264ed35a3e26dc131c099eca45ac23dbc2e1a0d00f6defd6428a6431429b2
744943f2e1dffe00bbd1dcf22ec7c0dde553659763c8c11db883ccb6de0de91d
5d2bcffe57e368bf5a1799bbd6f978706793dc7aa710c1cf00725827df6651e2
15ca4bc83509c89bb257479a2833fa972f4344799c37f8217b704c9e5ae2e09d
1d5941ddd4caf71d12a823fdf421930df034220bd8ee37fc8b0543f1f2f49ade
6a7ffcc7ab9d1edab4b07b7f33a72f0c660ea3c46fd7c1243ed956244e506463 - publicExponent:
010001 - privateExponent:
a6c362cd98e2b5f295a66dec37f2d7951697837e78381b0ab12e39cb653785cf
8f33de7d151b398ba3bb1a65733c30be851785cfea96b94f5fd9a440e14c5fc4
099b06ecae566541097d95e28082d988f07cce8215360409b97f1837c1aa1f23
4f3902535a8132a73cd3748b3f4efbf18acd85a57fe3c4aca1cba7007daf2600
5ac200c6fbc7baac75eb4ddc25f40a911fb9f2e9e896177def1de96fbcf8563f
0d3ff0c6ca578b937f635db4dfd7375ecf2ddd3afd7ce7e27a01555e4de382c9
11e250b16045d9228e32be1d635cbf649a3c6b7ecf2fe65471dc7b1e219348f9
cb9393f480b9faa3d40d0f88441502a5912a7470b33cc1f4e42903d924b7f5d9 - prime1:
e03ec42723797e4ef903ce5d2b4576885f9c2fe0ab9c4cd79cb15f970b792472
4b1b65f3f8142311f48fcd6c16df881c58fbd67e234171a6f1c0285b439eea32
1342c42580eaa4431fb0181498922cbc169234630b6ad1f033127e4340ef1095
d42781e21992073f8f42bb844b5108a2ebb188252a858315f81843b89ad5ae87 - prime2:
dd6fa073b6ecdfaf0da10ab409c883a0147501afe5c3b8ab02ff5865c366d28f
c678b1c6af3c0d577ee03d12fc7f6fad298555044c11db602793f2aae4c542de
2f6c905bce239facad40c919866776c76d48fa684045d2d804127fc637d9ebb0
9ffd5994512caaa3193f8ddc2676551b5abb70c7732ac12759e0c0d8dbf15645 - exponent1:
550ffa204e989b8d21708c2b536aba17e90cba2ca36c5ac9bf2a9974166a11a5
39505f50385e8b1f1882240e486eea96b63a7196cf90d7a7d834681a9680059e
9127d677d37b2e6c37ecf875779a9b558dca500cf21bc71f3280655ce598c9d5
cbf060987fd2a0e53f56b502edff0323a9fc62049728a61d034b510509d6dca9 - exponent2:
d077dde3f2ac30ae3a3389c3138ecdb4706df387a8d5494ede848cb14973ccfa
048cee3932126431224673d92313ca8c8891790791a22218f549c8e4f07971c9
817640b5dd6d164f57d0ad42b5914476ddc11dd5f5e4866a4df3288df158dd16
2c9934b3787487b502f91d51cc780d09b2b2d2ab4316563ff8d2aa5bbf3d06cd - coefficient:
46573748247030d0fc2fd9b602e7a0e26ef50509571d97e1c9bcb750b154d08a
1e75fac22e3f521a6d52da0950c1b322fd0ecb55014bd0ec328ce6b6a342dc9d
048d7488ad9d3db722fa450049f27a1584905170f7ce42eab1197d1df6c819f6
0066b987fc1e53b77ce865fcae091121b8b8c93457b85bb9d6d331e525f6729d
二、組裝PEM檔案
- 按照以上資料域順序依次組裝成TLV。
①version組裝
020100
說明:
02 – tag
01 – length
00 – value(version)
② modulus組裝
0282010100
c1f7f7196d9ef4b97abede2d5322d76c17fdf9592c39511027268293a14603b6
5d5425c99cfb5194d37b73487d26e31edf35cfe1e7f58366b5adb35d18f8cdb1
401264ed35a3e26dc131c099eca45ac23dbc2e1a0d00f6defd6428a6431429b2
744943f2e1dffe00bbd1dcf22ec7c0dde553659763c8c11db883ccb6de0de91d
5d2bcffe57e368bf5a1799bbd6f978706793dc7aa710c1cf00725827df6651e2
15ca4bc83509c89bb257479a2833fa972f4344799c37f8217b704c9e5ae2e09d
1d5941ddd4caf71d12a823fdf421930df034220bd8ee37fc8b0543f1f2f49ade
6a7ffcc7ab9d1edab4b07b7f33a72f0c660ea3c46fd7c1243ed956244e506463
說明:
02 – tag
82 – 81代表長度用1byte表示,82代表長度用2byte表示(此位元組部分tag後不存在)
0101 – length 2bytes表示
00 – 在modulus資料前新增00,原因未知,請知情道友告知。
③publicExponent組裝
0203010001
④privateExponent組裝
0282010100
a6c362cd98e2b5f295a66dec37f2d7951697837e78381b0ab12e39cb653785cf
8f33de7d151b398ba3bb1a65733c30be851785cfea96b94f5fd9a440e14c5fc4
099b06ecae566541097d95e28082d988f07cce8215360409b97f1837c1aa1f23
4f3902535a8132a73cd3748b3f4efbf18acd85a57fe3c4aca1cba7007daf2600
5ac200c6fbc7baac75eb4ddc25f40a911fb9f2e9e896177def1de96fbcf8563f
0d3ff0c6ca578b937f635db4dfd7375ecf2ddd3afd7ce7e27a01555e4de382c9
11e250b16045d9228e32be1d635cbf649a3c6b7ecf2fe65471dc7b1e219348f9
cb9393f480b9faa3d40d0f88441502a5912a7470b33cc1f4e42903d924b7f5d9
⑤prime1組裝
02818100
e03ec42723797e4ef903ce5d2b4576885f9c2fe0ab9c4cd79cb15f970b792472
4b1b65f3f8142311f48fcd6c16df881c58fbd67e234171a6f1c0285b439eea32
1342c42580eaa4431fb0181498922cbc169234630b6ad1f033127e4340ef1095
d42781e21992073f8f42bb844b5108a2ebb188252a858315f81843b89ad5ae87
⑥prime2組裝
02818100
dd6fa073b6ecdfaf0da10ab409c883a0147501afe5c3b8ab02ff5865c366d28f
c678b1c6af3c0d577ee03d12fc7f6fad298555044c11db602793f2aae4c542de
2f6c905bce239facad40c919866776c76d48fa684045d2d804127fc637d9ebb0
9ffd5994512caaa3193f8ddc2676551b5abb70c7732ac12759e0c0d8dbf15645
⑦exponent1組裝
028180
550ffa204e989b8d21708c2b536aba17e90cba2ca36c5ac9bf2a9974166a11a5
39505f50385e8b1f1882240e486eea96b63a7196cf90d7a7d834681a9680059e
9127d677d37b2e6c37ecf875779a9b558dca500cf21bc71f3280655ce598c9d5
cbf060987fd2a0e53f56b502edff0323a9fc62049728a61d034b510509d6dca9
⑧exponent2組裝
02818100
d077dde3f2ac30ae3a3389c3138ecdb4706df387a8d5494ede848cb14973ccfa
048cee3932126431224673d92313ca8c8891790791a22218f549c8e4f07971c9
817640b5dd6d164f57d0ad42b5914476ddc11dd5f5e4866a4df3288df158dd1
⑨coefficient組裝
028180
46573748247030d0fc2fd9b602e7a0e26ef50509571d97e1c9bcb750b154d08a
1e75fac22e3f521a6d52da0950c1b322fd0ecb55014bd0ec328ce6b6a342dc9d
048d7488ad9d3db722fa450049f27a1584905170f7ce42eab1197d1df6c819f6
0066b987fc1e53b77ce865fcae091121b8b8c93457b85bb9d6d331e525f6729d
- 輸出PEM檔案
①輸出以上資料域的總TLV:308204a4到PEM檔案;
②依次輸出以上組裝後的資料到PEM檔案。
至此,PEM檔案已生成。
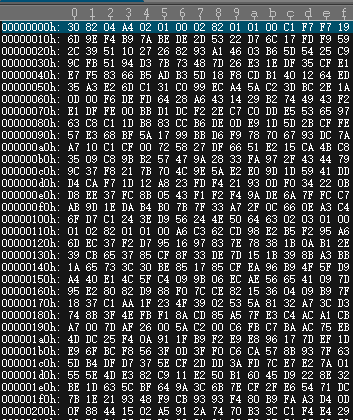
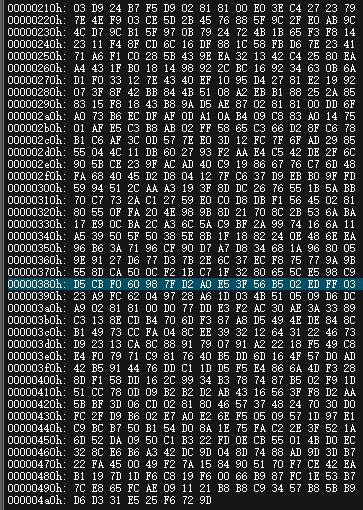
本文例項資料對應PEM檔案,如圖:
對此PEM檔案進行Base64編碼,即得到RSA私鑰:
—–BEGIN RSA PRIVATE KEY—–
MIIEpAIBAAKCAQEAwff3GW2e9Ll6vt4tUyLXbBf9+VksOVEQJyaCk6FGA7ZdVCXJ
nPtRlNN7c0h9JuMe3zXP4ef1g2a1rbNdGPjNsUASZO01o+JtwTHAmeykWsI9vC4a
DQD23v1kKKZDFCmydElD8uHf/gC70dzyLsfA3eVTZZdjyMEduIPMtt4N6R1dK8/+
V+Nov1oXmbvW+XhwZ5PceqcQwc8Aclgn32ZR4hXKS8g1CcibsldHmigz+pcvQ0R5
nDf4IXtwTJ5a4uCdHVlB3dTK9x0SqCP99CGTDfA0IgvY7jf8iwVD8fL0mt5qf/zH
q50e2rSwe38zpy8MZg6jxG/XwSQ+2VYkTlBkYwIDAQABAoIBAQCmw2LNmOK18pWm
bew38teVFpeDfng4GwqxLjnLZTeFz48z3n0VGzmLo7saZXM8ML6FF4XP6pa5T1/Z
pEDhTF/ECZsG7K5WZUEJfZXigILZiPB8zoIVNgQJuX8YN8GqHyNPOQJTWoEypzzT
dIs/Tvvxis2FpX/jxKyhy6cAfa8mAFrCAMb7x7qsdetN3CX0CpEfufLp6JYXfe8d
6W+8+FY/DT/wxspXi5N/Y12039c3Xs8t3Tr9fOfiegFVXk3jgskR4lCxYEXZIo4y
vh1jXL9kmjxrfs8v5lRx3HseIZNI+cuTk/SAufqj1A0PiEQVAqWRKnRwszzB9OQp
A9kkt/XZAoGBAOA+xCcjeX5O+QPOXStFdohfnC/gq5xM15yxX5cLeSRySxtl8/gU
IxH0j81sFt+IHFj71n4jQXGm8cAoW0Oe6jITQsQlgOqkQx+wGBSYkiy8FpI0Ywtq
0fAzEn5DQO8QldQngeIZkgc/j0K7hEtRCKLrsYglKoWDFfgYQ7ia1a6HAoGBAN1v
oHO27N+vDaEKtAnIg6AUdQGv5cO4qwL/WGXDZtKPxnixxq88DVd+4D0S/H9vrSmF
VQRMEdtgJ5PyquTFQt4vbJBbziOfrK1AyRmGZ3bHbUj6aEBF0tgEEn/GN9nrsJ/9
WZRRLKqjGT+N3CZ2VRtau3DHcyrBJ1ngwNjb8VZFAoGAVQ/6IE6Ym40hcIwrU2q6
F+kMuiyjbFrJvyqZdBZqEaU5UF9QOF6LHxiCJA5IbuqWtjpxls+Q16fYNGgaloAF
npEn1nfTey5sN+z4dXeam1WNylAM8hvHHzKAZVzlmMnVy/BgmH/SoOU/VrUC7f8D
I6n8YgSXKKYdA0tRBQnW3KkCgYEA0Hfd4/KsMK46M4nDE47NtHBt84eo1UlO3oSM
sUlzzPoEjO45MhJkMSJGc9kjE8qMiJF5B5GiIhj1Scjk8HlxyYF2QLXdbRZPV9Ct
QrWRRHbdwR3V9eSGak3zKI3xWN0WLJk0s3h0h7UC+R1RzHgNCbKy0qtDFlY/+NKq
W789Bs0CgYBGVzdIJHAw0Pwv2bYC56DibvUFCVcdl+HJvLdQsVTQih51+sIuP1Ia
bVLaCVDBsyL9DstVAUvQ7DKM5rajQtydBI10iK2dPbci+kUASfJ6FYSQUXD3zkLq
sRl9HfbIGfYAZrmH/B5Tt3zoZfyuCREhuLjJNFe4W7nW0zHlJfZynQ==
—–END RSA PRIVATE KEY—–
三、通過OpenSSL命令,獲得私鑰中各個引數的值:
命令:openssl rsa -in private_rsa.pem -text -out private.txt
然後就可以在private.txt檔案中檢視RSA金鑰中各個引數的值